Monitor
Visibility across the internet including the deep and dark web
Anticipate
Early warning of malicious targeting and potential attacks
Detect
Early notice of breaches or data or credential leaks from internal and external sources
Focus on what’s important
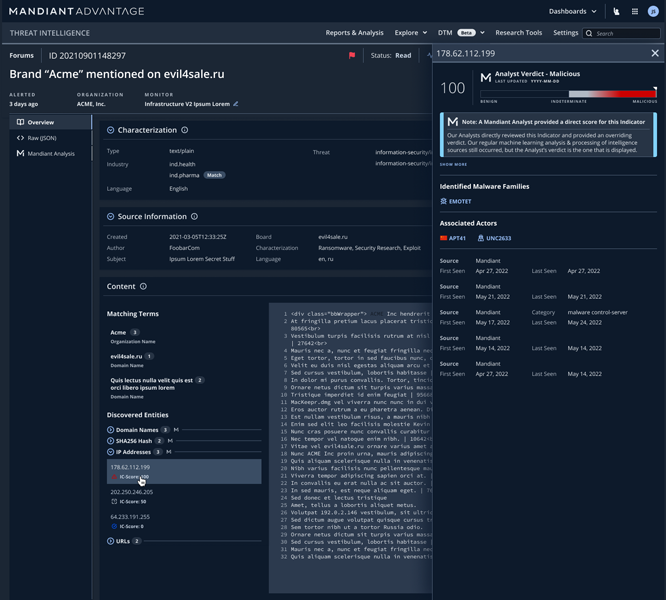
Your security tools create alerts all day. Unfortunately, many of these alerts are false positives or low priority alerts. Digital Threat Monitoring uses machine learning to extract actionable information from our stream of proprietary threat intelligence and combine it with frontline knowledge. The result is higher quality alerts and less wasted time.
Open web
Also known as the surface or clear web, this is easily accessible data indexed by search engines–but it only comprises 10% of available information
Deep web
Most online information falls into this category, were data is not indexed by search engines; this includes academic networks and information that requires payment or registration.
Dark web
This section of the Internet requires special software (such as TOR) and configurations to access and criminal forums and marketplaces are typically hosted here (the "underground").
Brand
Prevent the loss of customers, revenue, and trust
VIPs
Prevent targeted attacks and better mitigate hacktivism
Technical resources
Mitigate extortion and data loss
Trusted relationships
Prevent a conduit to a data breach or disruption of your supply chain
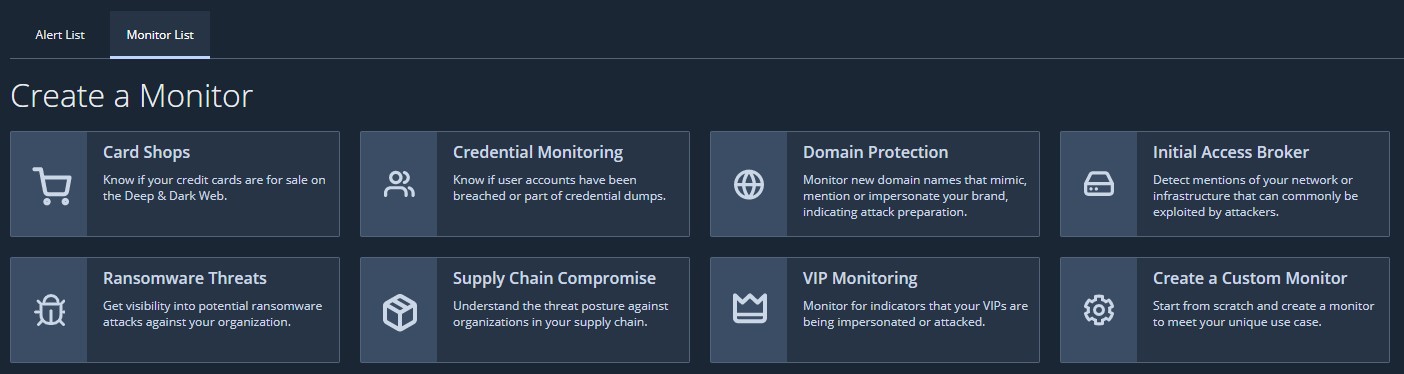
Templated monitors simplify the setup and tuning process. These pre-configured templates will help ensure your monitors for keywords are effective from the beginning reducing false positives and negatives.
Uplevel Your Security Team with a Digital Risk Protection Solution
Learn what a digital risk protection solution is and how it can help you be better prepared by understanding who is targeting you, what they’re after, and how they plan to compromise you.
Strengthen Your Cyber Risk Profile with Mandiant
Learn how a digital risk protection solution gives you visibility into your global attack surface and dark web activity and builds a complete cyber threat profile.
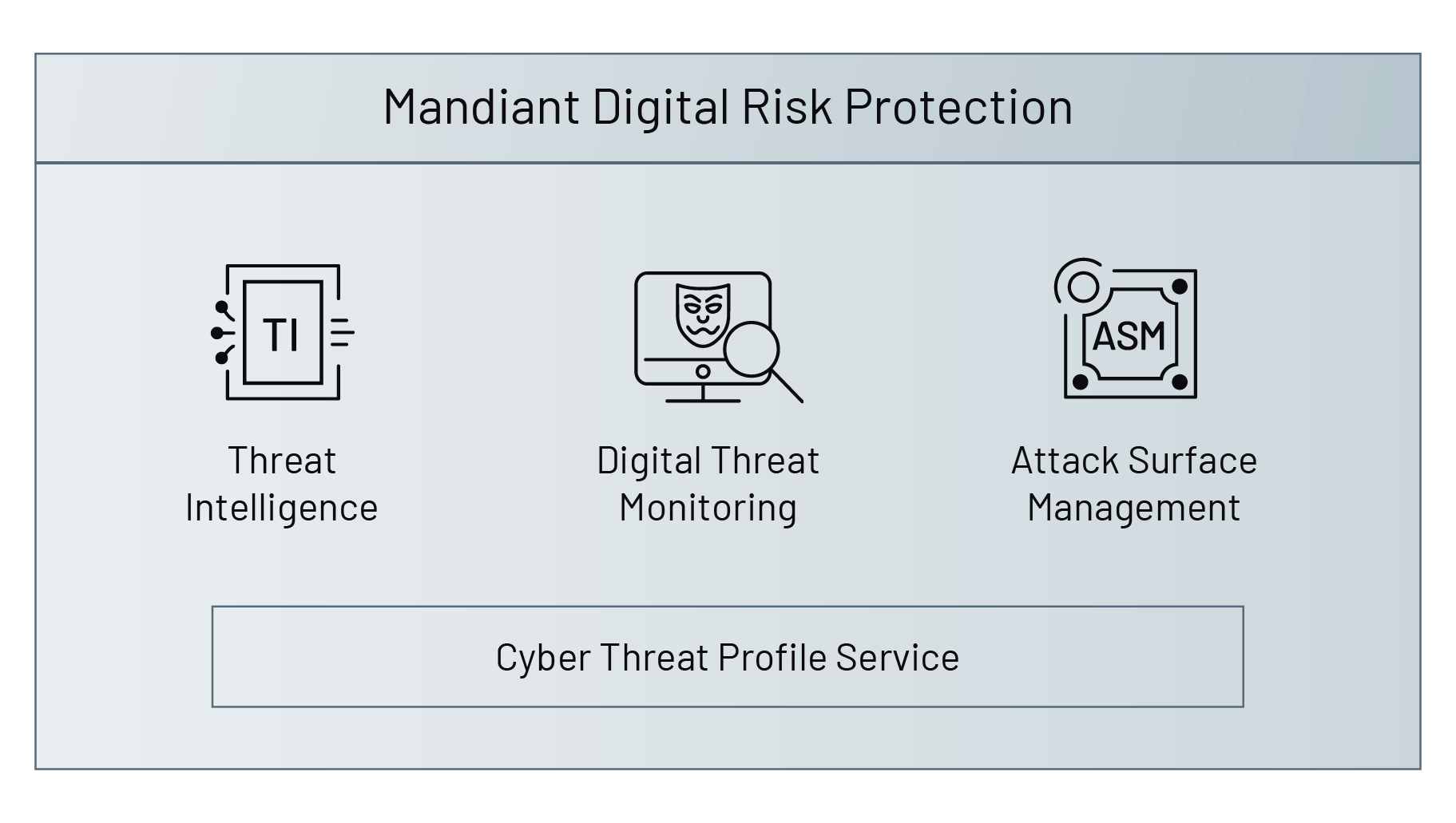
Threat Intelligence
Understand the threats Mandiant sees targeting you and your peers
Attack Surface Management
See your organization through the eyes of an attacker
Cyber Threat Profile
Make security decisions based on the threats that matter most

